Princeton University
Princeton Weekly Bulletin October 2, 2006, Vol. 96, No. 4 prev next current
- Page One
- • Princeton establishes leading research computing facility
- • Progress on grading policy continues, data show no drawbacks for graduates
- Inside
- • Upgrades bring faster, broader networking to campus
- • Researchers reveal vulnerabilities in e-voting machines
- • Communications, development offices win national awards
- • Faculty to give President’s Lectures
- • Series explores presidential leadership in times of crisis
- Almanac
- • Calendar of events
- • Nassau notes
- • By the numbers
- The Bulletin is published weekly during the academic year, except during University breaks and exam weeks, by the Office of Communications. Second class postage paid at Princeton. Postmaster: Send address changes to Princeton Weekly Bulletin, Office of Communications, Princeton University, 22 Chambers St., Suite 201, Princeton, NJ 08542. Permission is given to adapt, reprint or excerpt material from the Bulletin for use in other media.
- Subscriptions. The Bulletin is distributed free to faculty, staff and students. Others may subscribe to the Bulletin for $30 for the 2006-07 academic year (half price for current Princeton parents and people over 65). Send a check to Office of Communications, Princeton University, 22 Chambers St., Suite 201, Princeton, NJ 08542.
- Deadlines. In general, the copy deadline for each issue is the Friday 10 days in advance of the Monday cover date. The deadline for the Bulletin that covers Oct. 16-22 is Friday, Oct. 6. A complete publication schedule is available at www.princeton.edu/ pr/ pwb/ deadlines.html; or by calling (609) 258-3601.
- Editor: Ruth Stevens Calendar editor: Carolyn Geller Staff writers: Jennifer Greenstein Altmann, Eric Quiñones Contributing writers: Chad Boutin, Cass Cliatt, Karin Dienst, Teresa Riordan Photographers: Denise Applewhite, John Jameson Design: Maggie Westergaard Web edition: Mahlon Lovett
Researchers reveal vulnerabilities in e-voting machines
Princeton NJ — In a paper recently published on the Web, a group of Princeton computer scientists said they created demonstration vote-stealing software that can be installed within a minute on a common electronic voting machine. The software can fraudulently change vote counts without being detected.
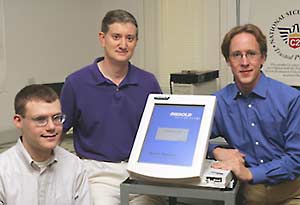
Edward Felten (center), director of the Center for Information Technology Policy, has co-written a paper with graduate students Ariel Feldman (left) and Alex Halderman on a demonstration vote-stealing software that highlights security vulnerabilities in electronic voting machines. (photo: John Jameson)
“We have created and analyzed the code in the spirit of helping to guide public officials so that they can make wise decisions about how to secure elections,” said Edward Felten, the director of the Center for Information Technology Policy, a new center at Princeton that addresses crucial issues at the intersection of society and computer technology.
The paper appears on the Web site for the Center for Information Technology Policy at itpolicy.princeton.edu/voting/.
The researchers obtained the machine, a Diebold AccuVote-TS, from a private party in May. They spent the summer analyzing the machine and developing the vote-stealing demonstration.
“We found that the machine is vulnerable to a number of extremely serious attacks that undermine the accuracy and credibility of the vote counts it produces,” wrote Felten and his co-authors, graduate students Ariel Feldman and Alex Halderman.
In a 10-minute video on their Web site, the researchers demonstrate how the vote-stealing software works. The video shows the software sabotaging a mock presidential election between George Washington and Benedict Arnold. Arnold is reported as the winner even though Washington gets more votes. (The video is edited from a longer continuously shot video; the long single-shot version will be available for downloading from the center’s site as well.)
The researchers also demonstrate how the machines “are susceptible to computer viruses that can spread themselves automatically and invisibly from machine to machine during normal pre- and post-election activity.”
Felten said that policy-makers should be concerned about malicious software infecting the Diebold AccuVote-TS and machines like it, from Diebold and other companies. “We studied these machines because they were available to us,” the researchers wrote in their Web posting. “If we had gotten access to another kind of machine, we probably would have studied it instead.”
Felten said, “There is reason for concern about other machines as well, even though our paper doesn’t directly evaluate them. Jurisdictions using these machines should think seriously about finding a backup system in time for the November elections.”
Felten, a professor of computer science and public affairs who is known for his groundbreaking work in computer security, said that some of the problems discussed in the paper cannot be fixed without completely redesigning the machine.
Other problems can be fixed by addressing software or electronic procedures. “But time is short before the next election,” he said.
According to the researchers’ paper, the Diebold machine they examined and another newer version are scheduled to be used in 357 U.S. counties representing nearly 10 percent of all registered voters. About half those counties, including all of Maryland and Georgia, will use the exact machine examined by Felten’s group.
Felten said that, out of security concerns, the Diebold machine infected with the vote-stealing software has been kept under lock and key in a secret location.
“Unfortunately election fraud has a rich history from ballot stuffing to dead people voting,” he said. “We want to make sure this doesn’t fall into the wrong hands. We also want to make sure that policy-makers stay a step ahead of those who might create similar software with ill intent.”
Princeton’s Center for Information Technology Policy encompasses members from diverse departments, including computer science, economics, electrical engineering, operations research and financial engineering, sociology and the Woodrow Wilson School of Public and International Affairs.